Getting started – Installing the ActiveRoles Management Shell for Active Directory
The Add-QADPermission command is a third party PowerShell command so you will need to first download and install the new commands from the Quest site on the computer that you will be running the PowerShell commands. You can download the Quest ActiveRoles Management Shell for Active Directory from here http://www.quest.com/PowerShell/activeroles-server.aspx and then install the MSI file.
Installing ActiveRoles Management Shell for Active Directory
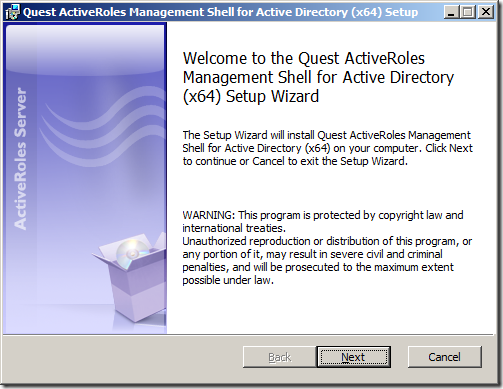
Step 1. After launching the MSI click “Nextâ€
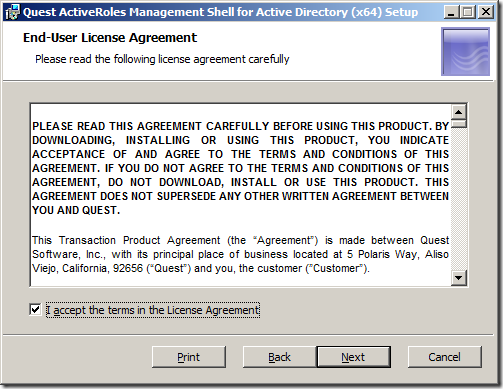
Step 2. Tick “I accept the terms in the Licence Agreement†and click “Nextâ€
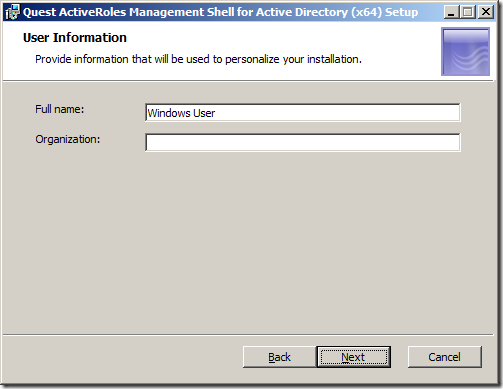
Step 2. 3lick “Nextâ€
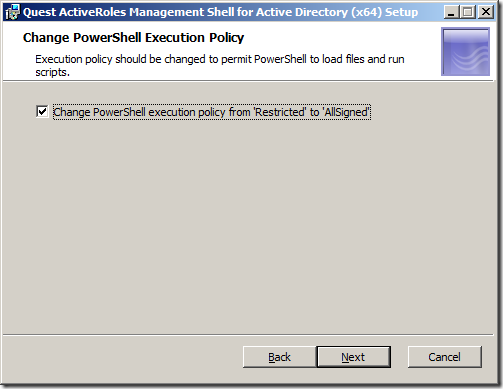
Step 4. Click “Nextâ€
Note: By ticking the “Change PowerShell execution policy from ‘Restricted’ to ‘AllSigned’ you are relaxing the execution policy of PowerShell. However you will still need to turn this off entirely for the testing of your script.
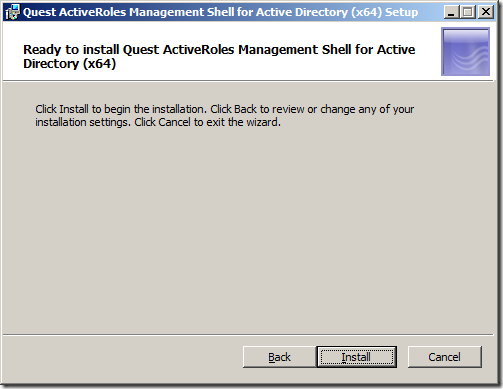
Step 5. Click “Installâ€
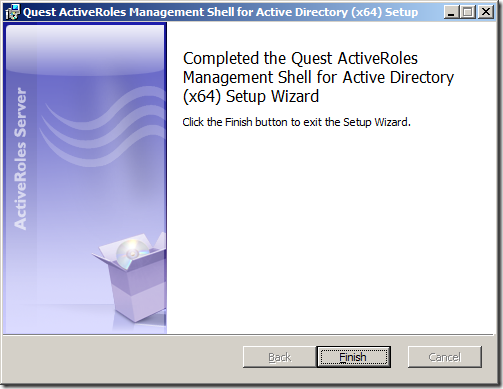
Step 6. Click “Finishâ€
You have now successfully install the Quest ActiveRoles Management Shell for Active Directory. Now it is time to use the new PowerShell Command.




Blog Post: How to delegate AD permission to Organisational Units using the PowerShell command Add-QADPermission http://bit.ly/dcXL9O
How to delegate AD permission to OUs using PowerShell. http://t.co/OGMAKjv via @grouppolicy_biz Good stuff that I might have to "borrow"
RT @alanburchill: Blog Post: How to delegate AD permission to Organisational Units using the PowerShell command Add-QADPermission http://bit.ly/dcXL9O
How to delegate AD permission to Organisational Units using the PowerShell command Add-QADPermission http://t.co/7RHgwWP
How to delegate AD permission to Organisational Units using the PowerShell command Add-QADPermission
Is your organization sensational? Is that why you spell it organisational?
You spell Organisation with an S in Australia…
Allan;
When I try to use the Add-QADPermission commandlet (following your example above) in a test environment I get the following error:
Add-QADPermission : The search filter is invalid.
At C:\WindowsPowerShell\test-it.ps1:33 char:18
+ Add-QADPermission <<<< -Identity "OU=New-OU,dc=XXX,dc=XXX=dc=XX,dc=XX" -Account "-XXXX Delegation of Authority\Security Role Groups\Role-Adm-Account-Management" -Rights GenericAll -ApplyTo ChildObjects -ApplyToType Group
+ CategoryInfo : NotSpecified: (:) [Add-QADPermission], LdapException
+ FullyQualifiedErrorId : System.DirectoryServices.Protocols.LdapException,Quest.ActiveRoles.ArsPowerShellSnapIn.Cmdlets.AddPermi
ssionCmdlet
I have tried both with and without the '-identity' parameter specified and with the input string as above and also in a variable.
I haven't run into any similar problems running other commandlets from the snapin but this one has me stumped. Any suggestions as to what I've got wrong.
Not sure if it is just how you typed it but… -Account “-XXXX Delegation of Authority\Security Role Groups\Role-Adm-Account-Management” appears to be wrong… there should not be more than one “\” in the group name…
Okay, now I get.
WARNING: Can’t lookup account for identity: ‘XXX.XXX.XX.XX\Role-Adm-Account-Management’
WARNING: No valid accounts specified. Searching permissions for all accounts.
WARNING: Can’t lookup object for identity: OU=New-OU,dc=XXX,dc=XXX=dc=XX,dc=XX
I’m running my testing at (this point) as Domain Admin in the test environment so why can’t I look up the identity?
Looks like you are not using a valid Netbios domain name… should only be 15 characters with no dots
Your post helped me a lot, but had some issues with delegating Reset Password Permission
Here is what I found out
The command: Add-QADPermission “OU=People,DC=Contoso,DC=Local†-Account “CONTOSO\User Operators†-ExtendedRight User-Change-Password -ApplyTo ChildObjects -ApplyToType User
need to be changed to
Add-QADPermission “OU=People,DC=Contoso,DC=Local†-Account “CONTOSO\User Operators†-ExtendedRight User-Force-Change-Password -ApplyTo ChildObjects -ApplyToType User
User-Change-Password
Permits changing password on user account.
User-Force-Change-Password
Permits reseting password on user account.
Reference: http://technet.microsoft.com/en-us/library/ff405676.aspx
If you use the delegation Wizard to delegate the Reset Password permission, you’ll find out the a get-qadpermission, returns RIGHTS: Reset Password, not Change Password
Hi to all, it’s in fact a pleasant for me
to go to see this site, it consists of valuable Information.
My homepage; pdf books
I can’t see a way to delegate control to an OR, i can easily do it for group.
These powershell extensions appear to no longer free since the company changed to One-Identity.
Instead its a 30 day trial.