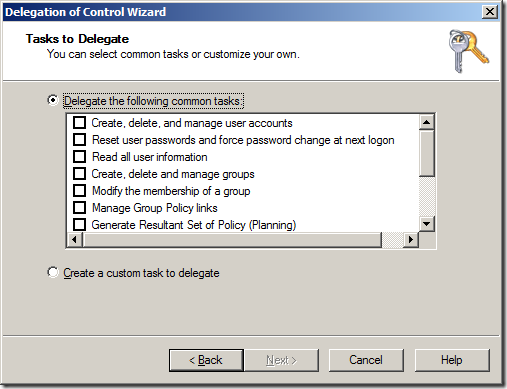
Recently, I have been working a lot with PowerShell to automate the creation of a full AD site OU structure (with Group Policy and all) along with all the necessary delegated permissions. One of the limitation of the out of the box AD PowerShell commands is there is no easy way (but apparently there is a really hard way) to delegate permission to Active Directory OU's. Luckily Quest Software have helped a lot here and they have offered a set of FREE PowerShell commands for Active Directory called "ActiveRoles Management Shell for Active Directory" one of which is called Add-QADPermission which greatly simplifies the process of delegation security in AD. The Add-QADPermission command can be used to add an DACL security descriptor permission to any AD object with a distinguished name such as users, computer or OU's. Therefore you can use this to delegate permission to OU similarly to running a "Delegation of Control Wizard" in Active Directory Users and Computers console (see image below). This wizard allows you to delegate some common tasks (see below) to your OU's in you Active Directory however the permissions they apply are not straight forward simple permissions. 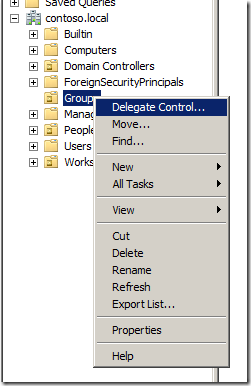 |
 |
|---|---|
| What I will show you how to do is how to perform some of the common delegation tasks that the "Delegation of Control Wizard" using a PowerShell command so you can automate the process for creating new OU's in your environment. I know this is not strictly an Group Policy topic but it is one closely related and one I think many Group Policy admins will find useful. The Command tasks I will show you are the one's that I almost exclusively use when delegating permissions to Active Directory, they are: |
- Create, delete and manage user accounts
- and Groups
- and Computers
- Reset user passwords and force password change at next logon
- Modify the membership of a group
Getting started — Installing the ActiveRoles Management Shell for Active Directory
The Add-QADPermission command is a third party PowerShell command so you will need to first download and install the new commands from the Quest site on the computer that you will be running the PowerShell commands. You can download the Quest ActiveRoles Management Shell for Active Directory from here http://www.quest.com/PowerShell/activeroles-server.aspx and then install the MSI file.
Installing ActiveRoles Management Shell for Active Directory
Step 1. After launching the MSI click "Next" 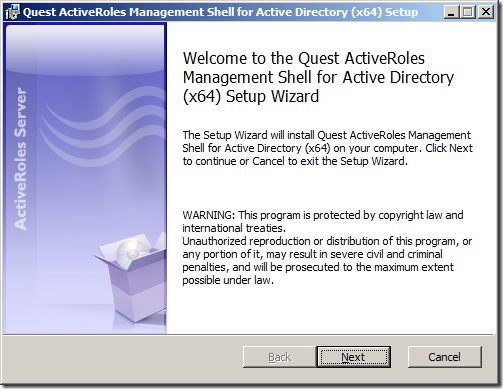 Step 2. Tick "I accept the terms in the Licence Agreement" and click "Next"
Step 2. Tick "I accept the terms in the Licence Agreement" and click "Next" 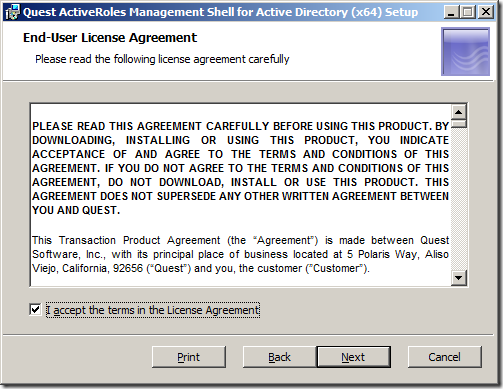 Step 2. 3lick "Next"
Step 2. 3lick "Next" 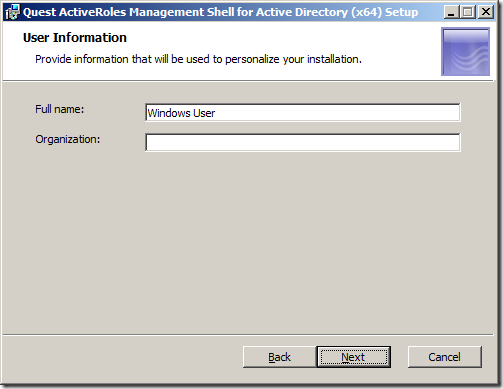 Step 4. Click "Next" Note: By ticking the "Change PowerShell execution policy from 'Restricted' to 'AllSigned' you are relaxing the execution policy of PowerShell. However you will still need to turn this off entirely for the testing of your script.
Step 4. Click "Next" Note: By ticking the "Change PowerShell execution policy from 'Restricted' to 'AllSigned' you are relaxing the execution policy of PowerShell. However you will still need to turn this off entirely for the testing of your script. 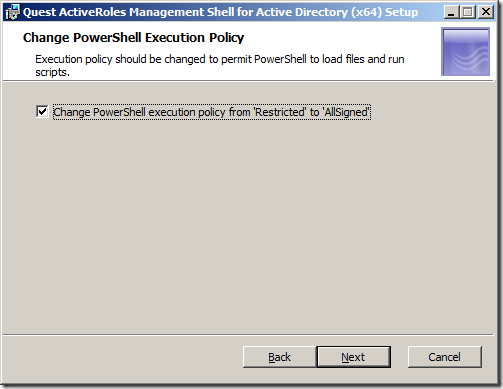 Step 5. Click "Install"
Step 5. Click "Install" 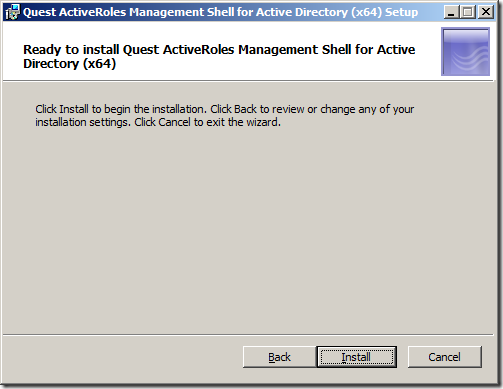 Step 6. Click "Finish"
Step 6. Click "Finish" 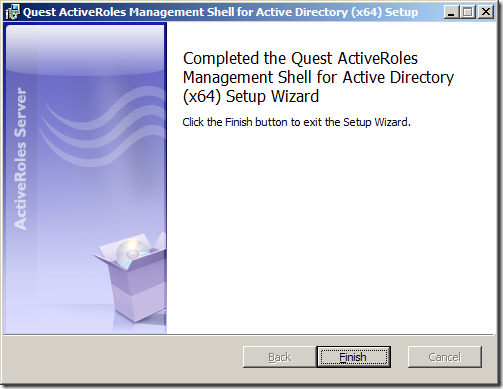 You have now successfully install the Quest ActiveRoles Management Shell for Active Directory. Now it is time to use the new PowerShell Command.
You have now successfully install the Quest ActiveRoles Management Shell for Active Directory. Now it is time to use the new PowerShell Command.
Running the add-QADPermission PowerShell command
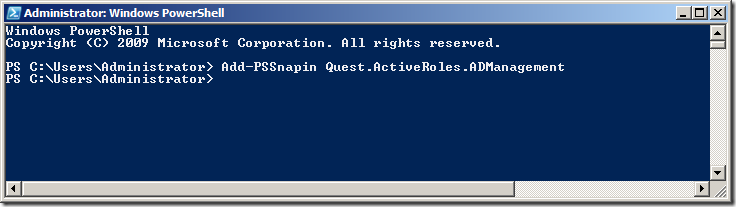
Step 1. To run the add-QADPermissions PowerShell command click on the PowerShell shortcut (that blue one in the taskbar if you are running 2008/R2).  Step 2. Run the command the following command to load the Quest PowerShell commands.
Step 2. Run the command the following command to load the Quest PowerShell commands.
Add-PSSnapin Quest.ActiveRoles.ADManagement
 Step 3. To test that the new PSSnapin is loaded type "add-qadper" and then press the "Tab" key to complete the command.
Step 3. To test that the new PSSnapin is loaded type "add-qadper" and then press the "Tab" key to complete the command. 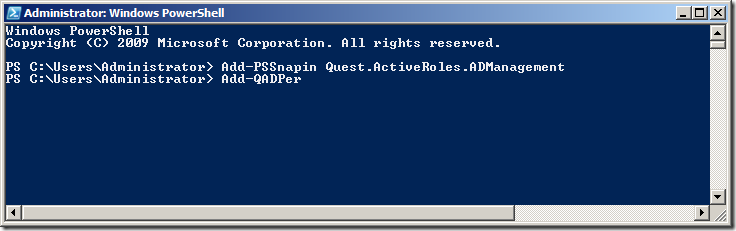 This should auto-complete the command to "Add-QADPermission"
This should auto-complete the command to "Add-QADPermission" 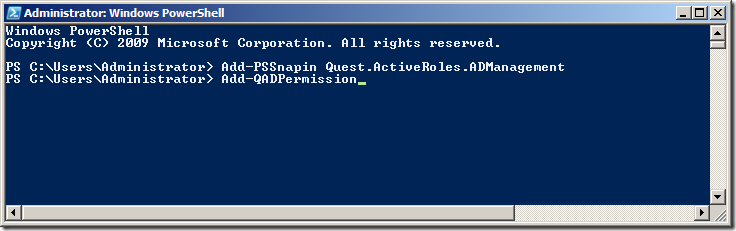 REMEMBER: Every time you launch a new PowerShell window you are going to need to run "Add-PSSnapin Quest.ActiveRoles.ADManagement" to load to load the Quest PowerShell Snapin's otherwise you will see a message like the image below.
REMEMBER: Every time you launch a new PowerShell window you are going to need to run "Add-PSSnapin Quest.ActiveRoles.ADManagement" to load to load the Quest PowerShell Snapin's otherwise you will see a message like the image below. 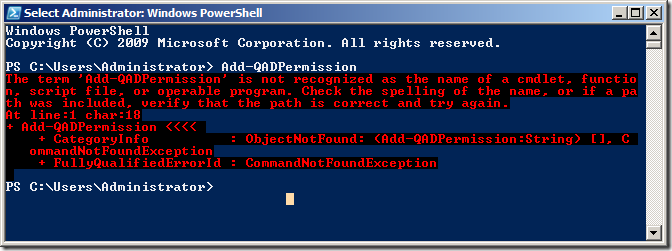 Now that we have verified that the new Quest AD PowerShell commands lets take a look at the command that will replicate some of the common tasks in the "Delegation of Control Wizard". In our example environment that we have an AD with three top level OU's called "People" "Groups" and "Workstations" (see below). These OU only contain the same type of objects that match the name of the OU (e.g. "People" contains User AD Objects) but it is possible to delegate all the permissions to the same single OU if it contains objects of multiple types (e.g. user,computers and groups).
Now that we have verified that the new Quest AD PowerShell commands lets take a look at the command that will replicate some of the common tasks in the "Delegation of Control Wizard". In our example environment that we have an AD with three top level OU's called "People" "Groups" and "Workstations" (see below). These OU only contain the same type of objects that match the name of the OU (e.g. "People" contains User AD Objects) but it is possible to delegate all the permissions to the same single OU if it contains objects of multiple types (e.g. user,computers and groups). 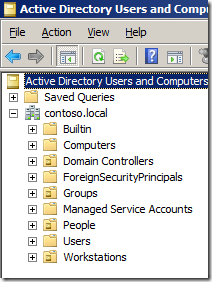
Delegating Create, delete and manage user accounts permissions using add-QADPermission
To delegate the same permission as the "Create, delete, and mange user accounts" (effectively Full Control) option in the "Delegation of Control Wizard" (see below) you need to delegate two permissions to the OU. 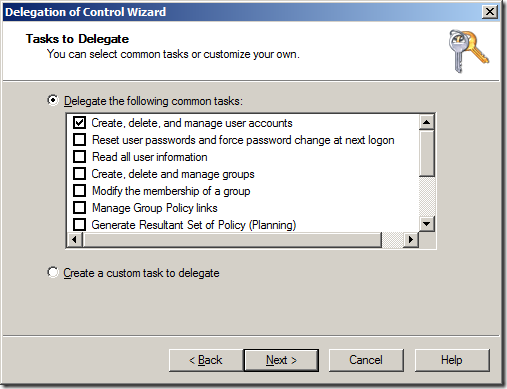
- Allow access to all the properties of the user objects
- Create / Delete permission of the user object
The first command will delegate Allow access to all the properties to the group called "User Admins" to all User objects in the OU with the distinguished name of "OU=People,DC=Contoso,DC=Local".
Add-QADPermission "OU=People,DC=Contoso,DC=Local" -Account "CONTOSO\User Admins" -Rights GenericAll -ApplyTo ChildObjects -ApplyToType User
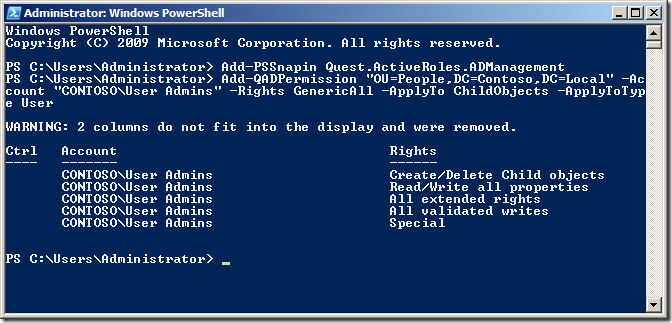 The second command will delegate Create / Delete permission for the User objects to the same OU for the same group.
The second command will delegate Create / Delete permission for the User objects to the same OU for the same group.
Add-QADPermission "OU=People,DC=Contoso,DC=Local" -Account "CONTOSO\User Admins" -Rights CreateChild,DeleteChild -ApplyTo All -ChildType User
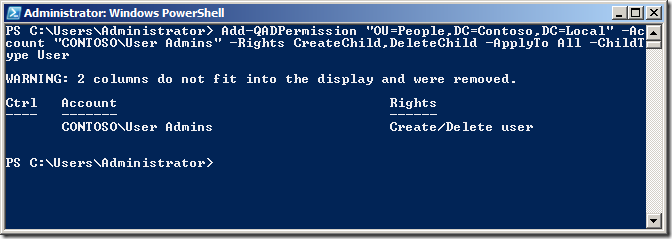 Now we can check the security on the People OU in Active Directory Users and Computer to verify the permission has been added correctly.
Now we can check the security on the People OU in Active Directory Users and Computer to verify the permission has been added correctly. 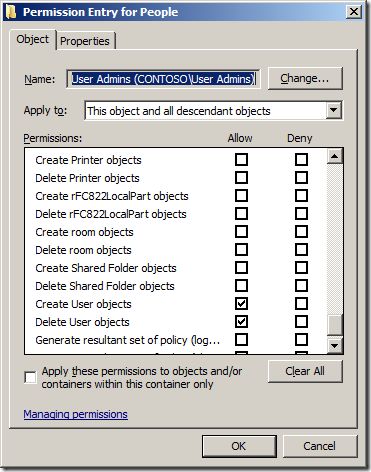
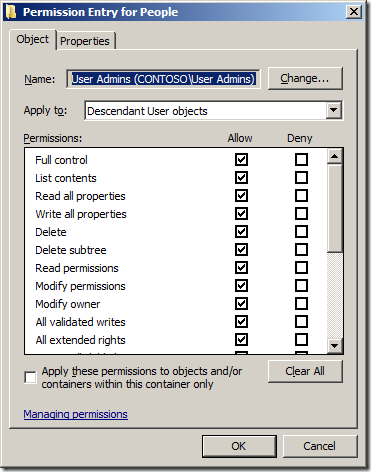 Note: See how we have used the "-ApplyTo ChildObjects" parameter and the "ApplyTo All" to ensure that these permission will inherit to all objects in this OU and sub-OU's. If the OU that you want to give the same Full Control permission to a Computers or Groups AD Object type all you need to do is change the -ApplyToType and -ChildType parameter to "computer" or "group" (See examples below)
Note: See how we have used the "-ApplyTo ChildObjects" parameter and the "ApplyTo All" to ensure that these permission will inherit to all objects in this OU and sub-OU's. If the OU that you want to give the same Full Control permission to a Computers or Groups AD Object type all you need to do is change the -ApplyToType and -ChildType parameter to "computer" or "group" (See examples below)
Example delegation Create, delete and manage (a.k.a. Full Control) Groups permissions using add-QADPermission
Add-QADPermission "OU=Workstations,DC=Contoso,DC=Local" -Account "CONTOSO\Workstations Admins" -Rights GenericAll -ApplyTo ChildObjects -ApplyToType Computer Add-QADPermission "OU=Workstations,DC=Contoso,DC=Local" -Account "CONTOSO\Workstations Admins" -Rights CreateChild,DeleteChild -ApplyTo All -ChildType Computer
Example delegation Create, delete and manage (a.k.a. Full Control) Computers permissions using add-QADPermission
Add-QADPermission "OU=Groups,DC=Contoso,DC=Local" -Account "CONTOSO\Groups Admins" -Rights GenericAll -ApplyTo ChildObjects -ApplyToType Group Add-QADPermission "OU=Groups,DC=Contoso,DC=Local" -Account "CONTOSO\Groups Admins" -Rights CreateChild,DeleteChild -ApplyTo All -ChildType Group
Delegating Reset user passwords and force password change at next logon using add-QADPermission
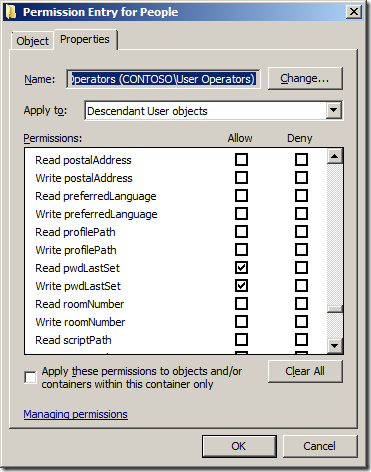
To delegate the same permission as the "Reset user passwords and force password change at next logon" option in the "Delegation of Control Wizard" (see below) you again need to delegate two permissions to the OU. ![image[48]](/uploads/2010/09/image48_thumb.png)
- Allow Read/Write to the Password Last Set Attribute
- Allow access to the "User-Change-Password" Extended Right
In this example we are going to delegate Allow Read and Write permission to the Pwd-Last-Set Attribute to all User objects to the OU with the distinguished name of "OU=People,DC=Contoso,DC=Local" to the group called "User Operators".
Add-QADPermission "OU=People,DC=Contoso,DC=Local" -Account "CONTOSO\User Operators" -Rights ReadProperty,WriteProperty -Property ('PwdLastSet') -ApplyTo ChildObjects -ApplyToType User
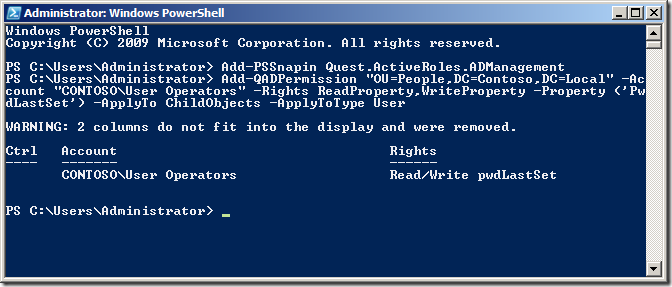 Now we are going to delegate permissions to the Extended Right User-Change-Password for the User objects to the same OU for the same group.
Now we are going to delegate permissions to the Extended Right User-Change-Password for the User objects to the same OU for the same group.
Add-QADPermission "OU=People,DC=Contoso,DC=Local" -Account "CONTOSO\User Operators" -ExtendedRight User-Change-Password -ApplyTo ChildObjects -ApplyToType User
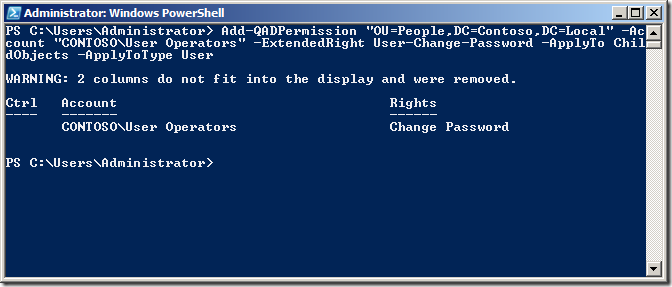 Again check the security on the People OU in Active Directory Users and Computer to verify the permission has been added correctly.
Again check the security on the People OU in Active Directory Users and Computer to verify the permission has been added correctly. 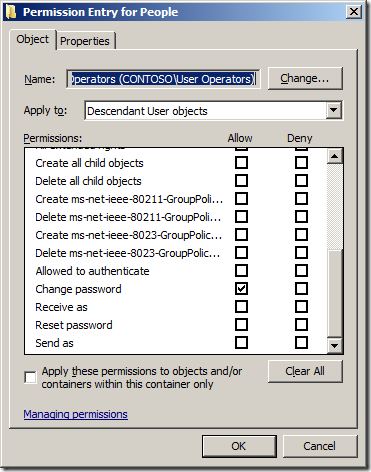
Delegating Modify the membership of a group using add-QADPermission
To delegate the same permission as the "Modify the membership of a group" option in the "Delegation of Control Wizard" (see below) you only need to apply one command to delegate the appropriate permissions. 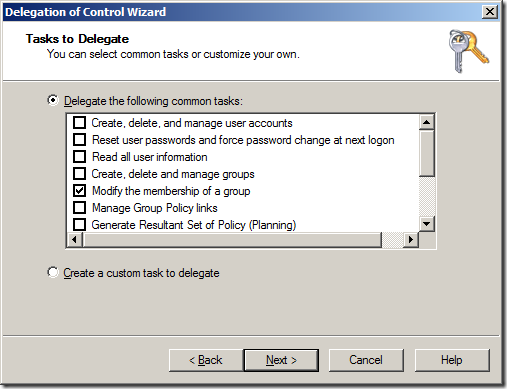
- Allow access to the Read/Write Members property on the Group
In this example we are going to delegate Change group membership permissions on all the Group objects to the OU with the distinguished name of "OU=Groups,DC=Contoso,DC=Local" to the group called "Group Operators"
Add-QADPermission "OU=Groups,DC=Contoso,DC=Local" -Account "CONTOSO\Group Operators" -Rights ReadProperty,WriteProperty -Property ('member') -ApplyTo ChildObjects -ApplyToType Group
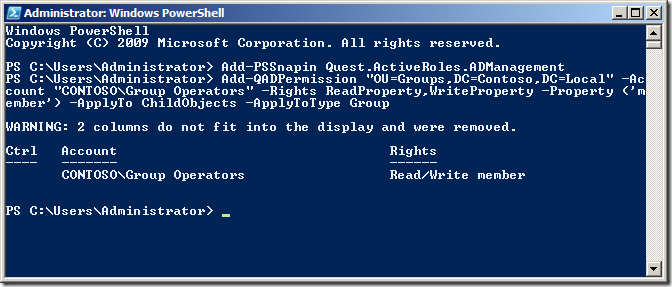 As always check the security on the People OU in Active Directory Users and Computer to verify the permission has been added correctly.
As always check the security on the People OU in Active Directory Users and Computer to verify the permission has been added correctly. 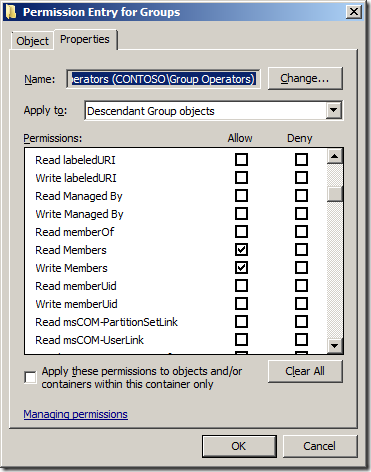
Summary
When used with the other out of the box AD PowerShell commands you should now be able to fully automate the creation AND delegation of permissions to a new OU structure for your environment.
References Sites
Below are some useful links to pages that show you how to use PowerShell when working with Active Directory.
- Automating Group Policy Management with Windows PowerShell
- PowerShell Get-ADUserGroupMembership
- Group Policy Team Blog: Group Policy & Scripting
- Group Policy Team Blog: PowerShell Script with GP cmdlets: Registry setting, Link
- TechNet: Active Directory Administration with Windows PowerShell
- MSDN Blog: Extending Active Directory Powershell
- The Experts Community: Delegating the PowerShell Way
Other AD Security Related Pages * TechNet: Access control in Active Directory * TechNet: Delegating administration * TechNet: Delegate Control of an Organizational Unit